Alice and Bob
Yash Soni / May 10, 2020
2 min read
Alice and Bob are fictional characters commonly used as a placeholder name in cryptology.
Alice and Bob first appeared in 1978 in a paper on cryptography. A method for obtaining digital signatures and public-key cryptosystems. They wrote
"For our scenarios we suppose that A and B (also known as Alice and Bob) are two users of a public-key cryptosystem".
Instead of saying "How can B send a private message M to A in a public-key cryptosystem?", they chose to represent it with more human friendly names Alice and Bob.
Within a few years, reference to Alice and Bob in cryptological literature became failry common and it even started to appear in Science and Engineering.
Cast of characters
The world of Alice and Bob grew with time and now there is a complete cast of characters serving some generic purpose.
| character name | usage |
|---|---|
| Alice and Bob | The original, generic characters. Generally, Alice and Bob want to exchange a message or cryptographic key. |
| Carol | The generic third participant. |
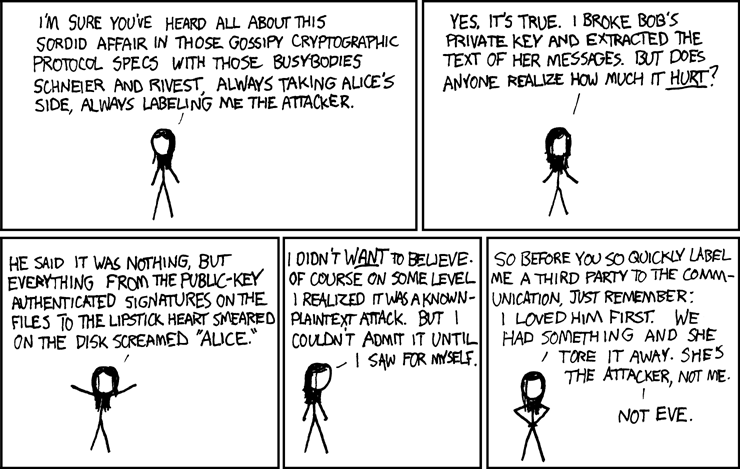
| Eve | The eavesdropper, who is usually a passive attacker |
| Grace | A government representative |
| Mallory | Malicious attacker. Unlike the passive Eve, Mallory/Mallet is an active attacker. usually participating in man-in-middle attacks |
| Trent | A trusted arbitrator, who acts as a neutral third party |